Bitcoin is more than digital gold — it’s a cryptographic marvel built on mathematical proofs, hashing algorithms, and decentralized consensus. This post breaks down how Bitcoin hashes work, why they’re essential for security, and what role different hashing functions like SHA‑256, PH, EH, and ZH play in the greater blockchain ecosystem.
📌 What Is a Hash? A Simple Introduction
A hash is a mathematical function that takes input data and produces a fixed‑length output, called a hash value or digest.
Imagine this like a unique fingerprint for data:
- Change 1 bit in the input ⇒ Completely different hash
- Input of any size ⇒ Same fixed‑length output
- One‑way function ⇒ You cannot reverse the hash to recover original data
Hash Key Properties
| Property | Description |
|---|---|
| Deterministic | Same input ⇒ Same hash |
| Fast to compute | Efficient for all input sizes |
| Pre‑image resistance | Hard to reverse |
| Collision resistance | Hard to find two inputs with same hash |
| Avalanche effect | Small change ⇒ Big hash difference |
These properties are critical for Bitcoin’s security and decentralized validation.
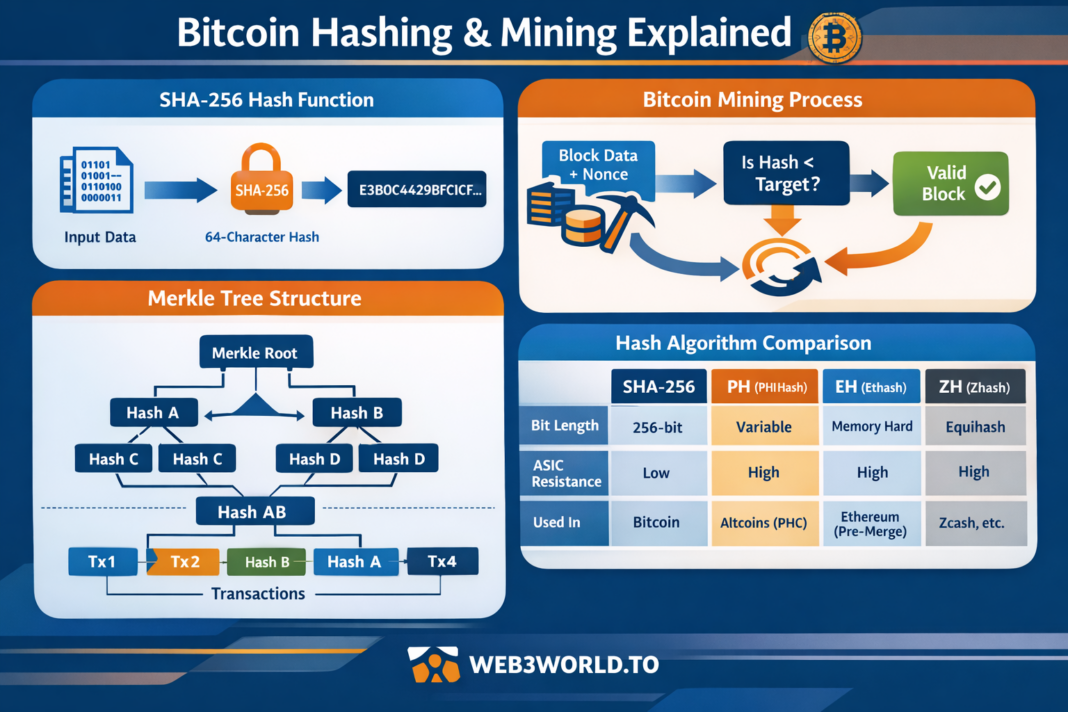
🔐 Bitcoin’s Main Hashing Function: SHA‑256
Bitcoin runs on SHA‑256 (Secure Hash Algorithm 256‑bit) — developed by the U.S. NSA and standardized by NIST.
SHA‑256 produces a 256‑bit (32‑byte) hash. In hexadecimal notation, that’s 64 characters.
✔️ Example (SHA‑256 of “Bitcoin”):
6d4503… (64 hex characters)
Why Bitcoin Uses SHA‑256
- Security: Extremely resistant to pre‑image and collision attacks
- Fixed output: Always 256 bits regardless of input size
- Hash puzzles: SHA‑256 enables proof‑of‑work (PoW)
💥 Bitcoin Mining: Hashing in Action
Bitcoin miners compete by hashing block header data using SHA‑256 over and over until they find a hash below a target threshold (difficulty).
How Mining Works
- Block header data (transactions + nonce + timestamp)
- Miner hashes using SHA‑256
- If hash < target ⇒ block valid
- If not ⇒ increment nonce and repeat
Because SHA‑256 outputs seem random, miners must brute‑force trillions of hashes per second.
💡 Hashrate (H/s) = How many hashes a machine computes per second
📉 Difficulty Adjustments
Bitcoin adjusts its difficulty every 2016 blocks (~2 weeks) so that blocks are found roughly every 10 minutes.
➡️ High hashrate ⇒ Difficulty ↑
➡️ Low hashrate ⇒ Difficulty ↓
This keeps block time stable and predictable — a cornerstone of Bitcoin’s economics.
🌐 Other Hash Types Mentioned in Crypto (PH, EH, ZH)
While Bitcoin uses SHA‑256, the wider blockchain space has diversified hashing algorithms to achieve different goals:
1) PH — PHI (e.g., PH‑Hash / PHC family)
Used in some privacy coins and altchains:
✔️ Designed to resist ASIC dominance
✔️ Memory‑hard design to favor CPUs/GPUs
✔️ Aims for egalitarian hashing
While not used in Bitcoin, PH variants influence decentralized mining strategies elsewhere.
2) EH — Ethash (Ethereum PoW)
Ethash (EH) is Ethereum’s PoW algorithm before the Merge:
✔️ Memory‑hard
✔️ ASIC‑resistant by design
✔️ Uses large dataset (DAG) to slow hashing
Ethash optimized mining for GPUs — contrasting Bitcoin’s SHA‑256 which favored ASIC mining.
3) ZH — Zhash (Equihash Variant)
Used in coins like Zcash:
✔️ Memory‑oriented
✔️ Equihash is a proof‑of‑work algorithm based on the generalized birthday problem
✔️ ASIC‑resistant
Equihash (and Zhash) helped some blockchains maintain decentralized mining distribution longer.
🛡️ Why Hashing Matters in Bitcoin Security
A. Tamper Evidence
Every block includes previous block’s hash.
Block 10 ⇒ contains hash of Block 9
Block 9 ⇒ contains hash of Block 8
Changing a single transaction would change all subsequent hashes — instantly detectable.
B. Merkle Trees
Transactions in a block are hashed and combined into a Merkle root:
Tx1, Tx2, … TxN → hashed pairwise → root
This allows:
- Efficient proofs of inclusion
- Light clients to verify transactions with minimal data
C. PoW & Consensus
SHA‑256 enables Bitcoin’s proof‑of‑work — a mechanism where:
✔️ Work is expensive
✔️ Results are easy to verify
This protects the network from attackers and ensures trustless consensus.
🚀 The Future: Post‑Quantum Hashing?
Quantum computers threaten asymmetric cryptography but hash functions like SHA‑256 remain safer longer.
Still, researchers are exploring:
✔️ Quantum‑resistant hash functions
✔️ Hybrid PoW/Sig schemes
Bitcoin upgrades here would require network consesus
📈 Final Thought
Hashing isn’t just math — it’s the secure backbone of Bitcoin’s decentralized trust.
From SHA‑256’s cryptographic strength to mining’s massive computational race, hashing makes Bitcoin:
✔️ Immutable
✔️ Secure
✔️ Verifiable
✔️ Decentralized